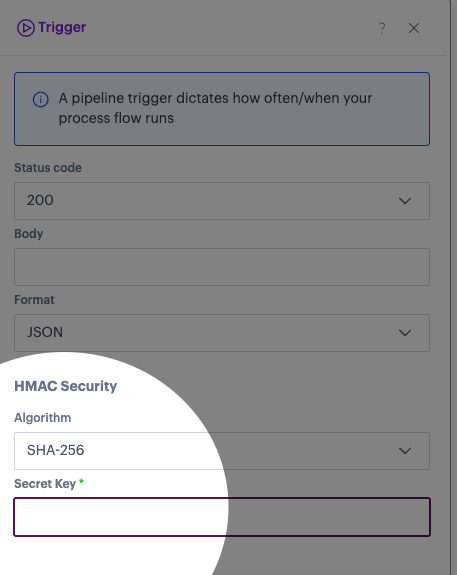
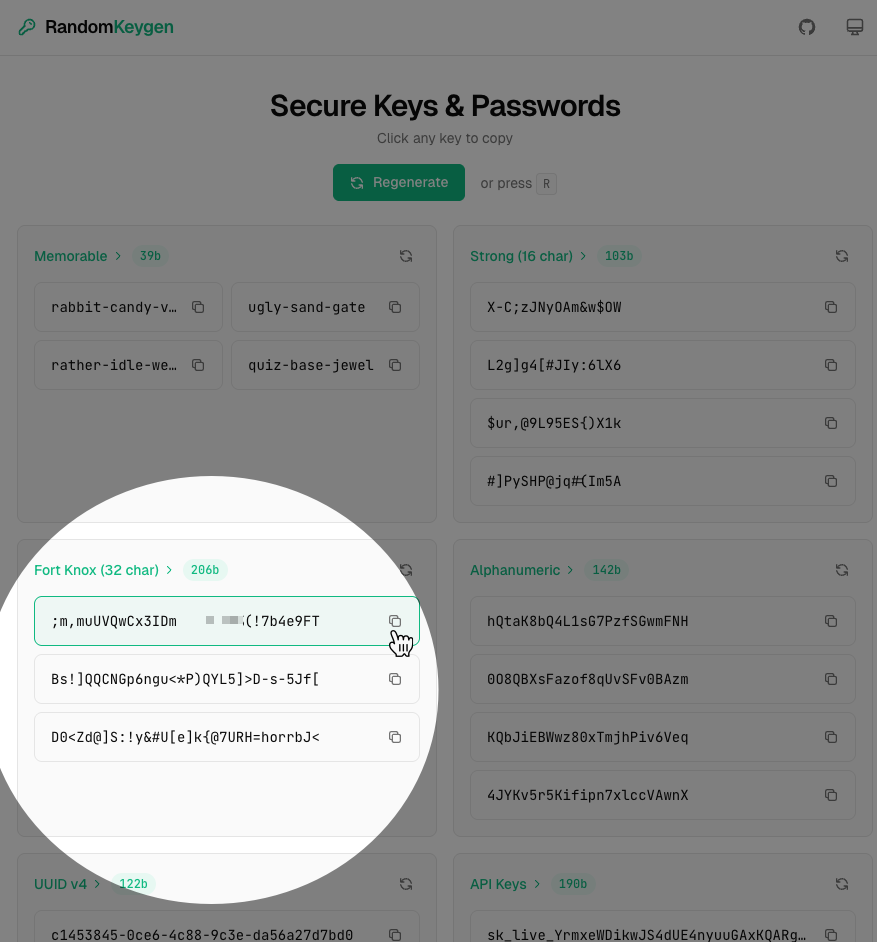
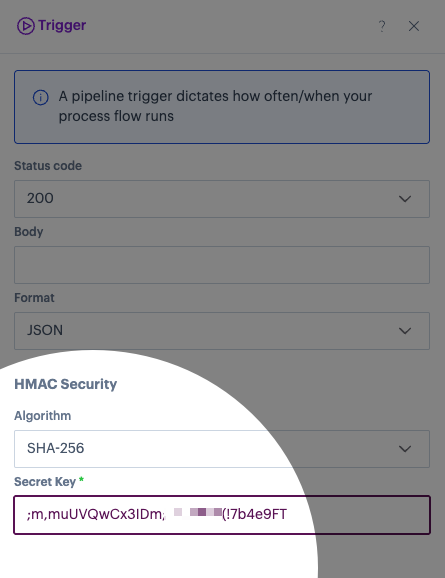
| Preparation | Patchworks and your third-party system both know a secret key. |
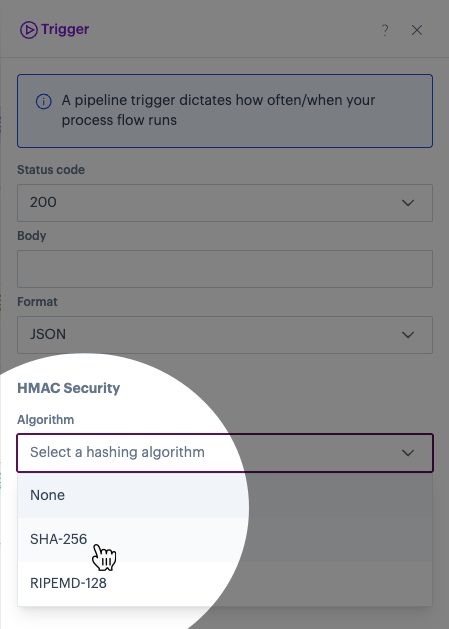
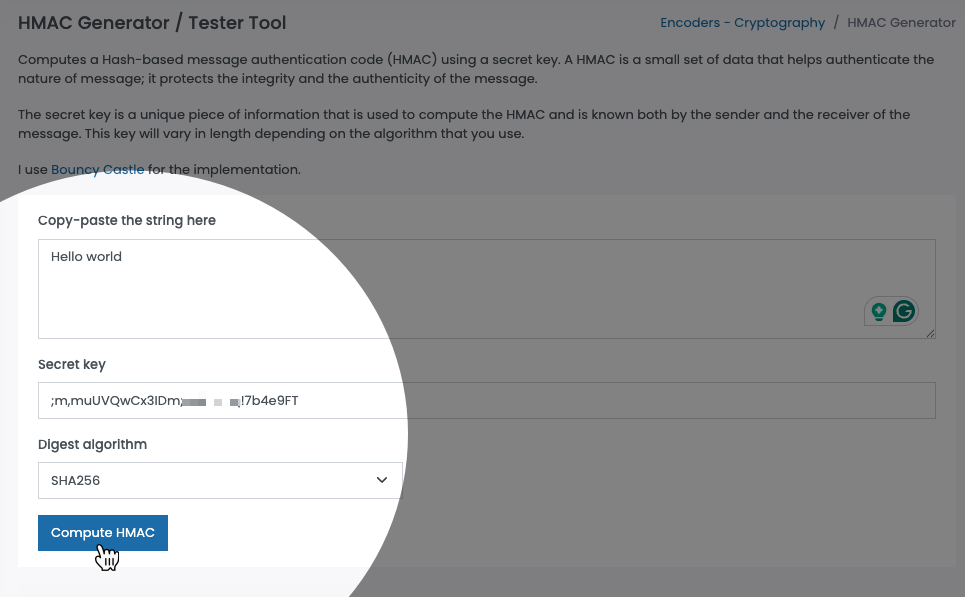
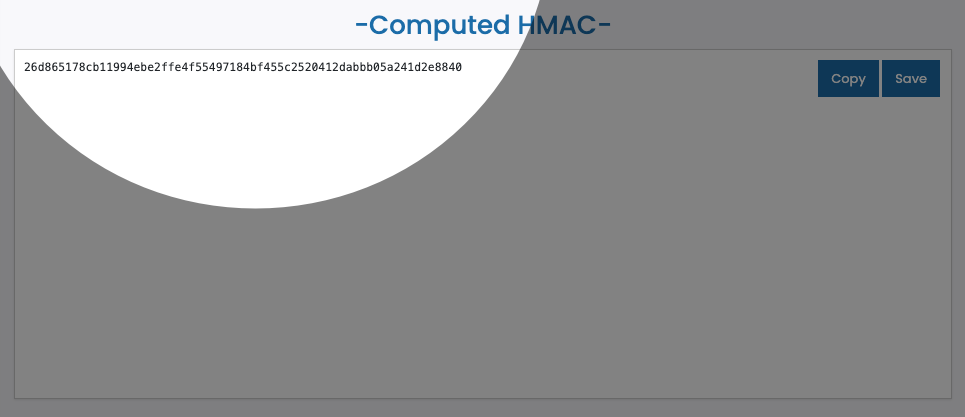
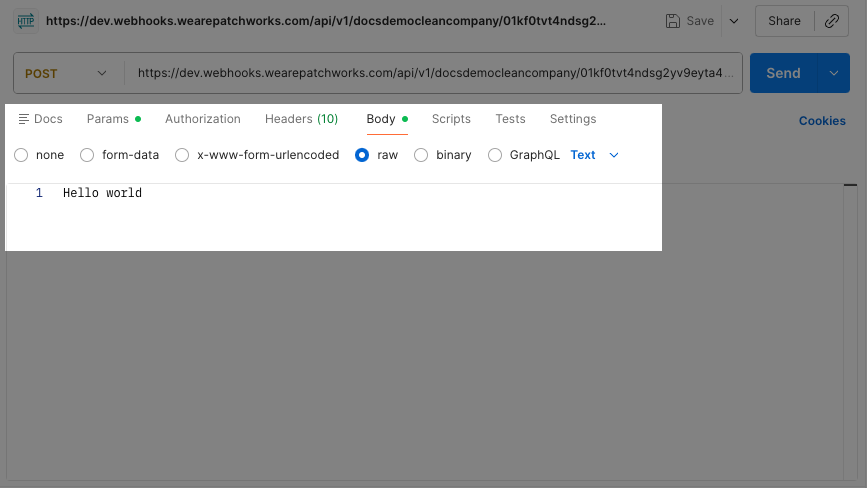
| Signing | When your third-party system prepares to POST a webhook, it runs the message body through a hashing algorithm (SHA-256 or RIPEMD-128), using the secret key. This produces a signature. |
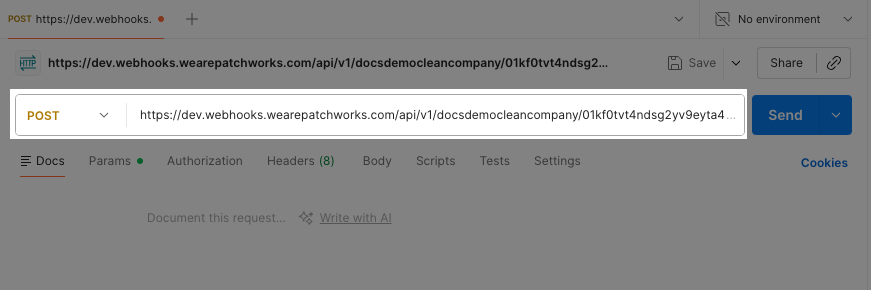
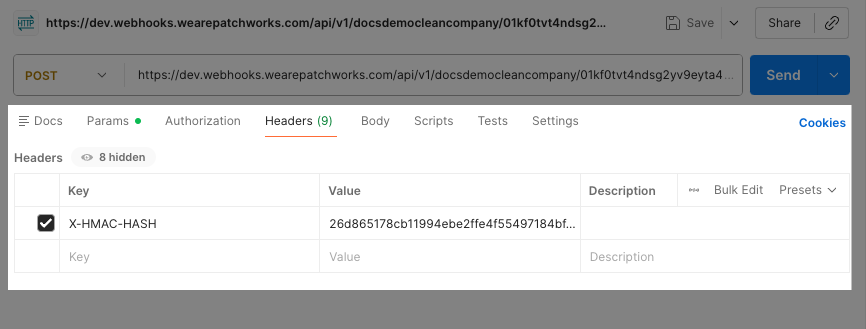
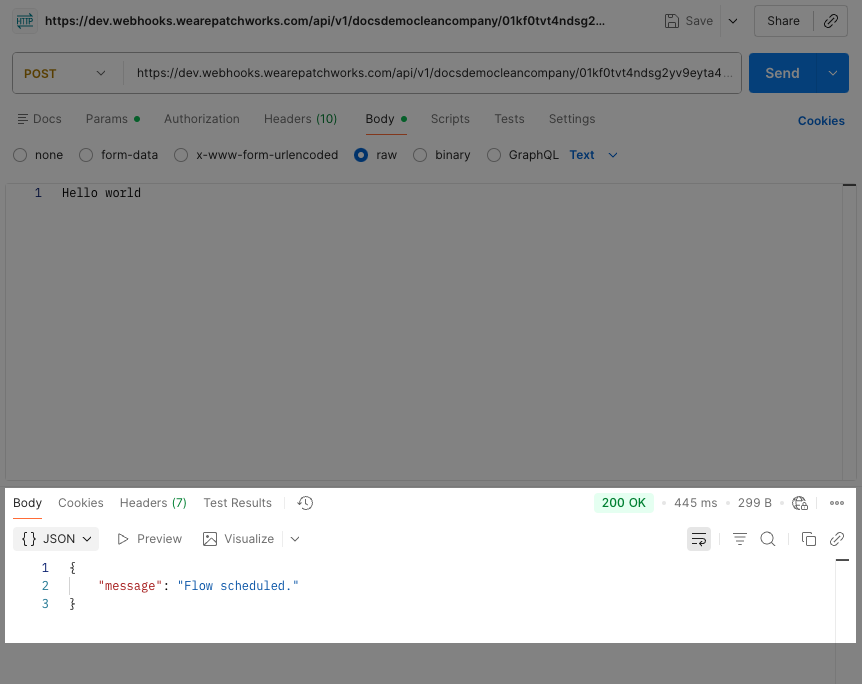
| Transmission | Your third-party system sends the data in the request body, and the signature, in an X-HMAC-HASH header. |
| Verification | When Patchworks receives the webhook, it takes the request body data and its own copy of your secret key and performs the same hashing calculation to verify that signatures match. If the signatures match, Patchworks knows the data is authentic and untampered. If they don't match, Patchworks rejects the request. |